...
- Existing installation on a LANCOM R&S®Unified Firewall with a firmware with LCOS FX as of version 10.8
- OpenVPN Client
- Apple iOS
- A configured and functional Internet connection on the Unified Firewall
- Web browser for configuring the Unified Firewall.
The following browsers are supported:- Google Chrome
- Chromium
...
| Info |
|---|
| This scenario also includes the “parallel” solution as described in the following this article. |
Procedure:
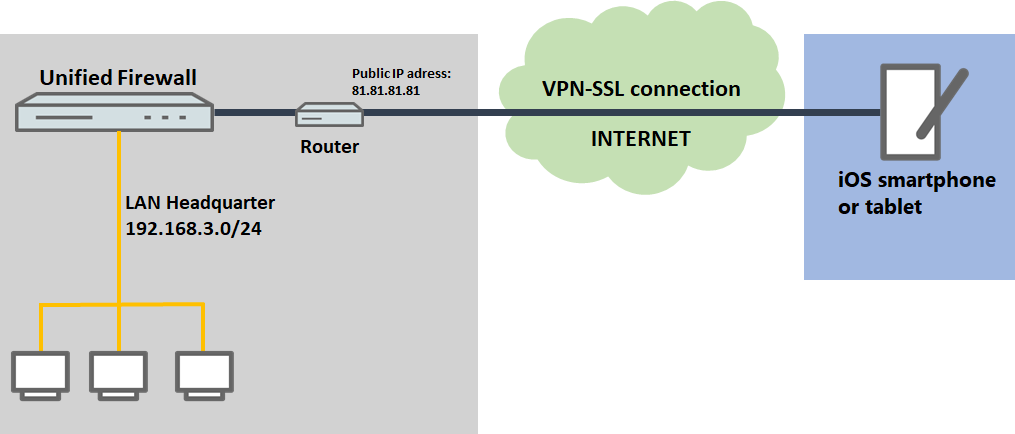
The setup for scenarios 1 and 2 are basically the same. Scenario 2 additionally requires port forwarding to be set up on the upstream router (see section 3).
...
- Certificate type: Select Certificate.
- Template: Select the template Certificate Authority.
- Common Name (CN): Enter a descriptive common name.
- Private key password: Set a password. This is used to encrypt the private key.
- Validity: Specify how long the certificate should remain valid. For a CA, the period of validity is usually set to be very high.
- Signing CA: From the drop-down menu, select the CA created in step 1.2.
- CA password: Enter the private key password set in step 1.2.
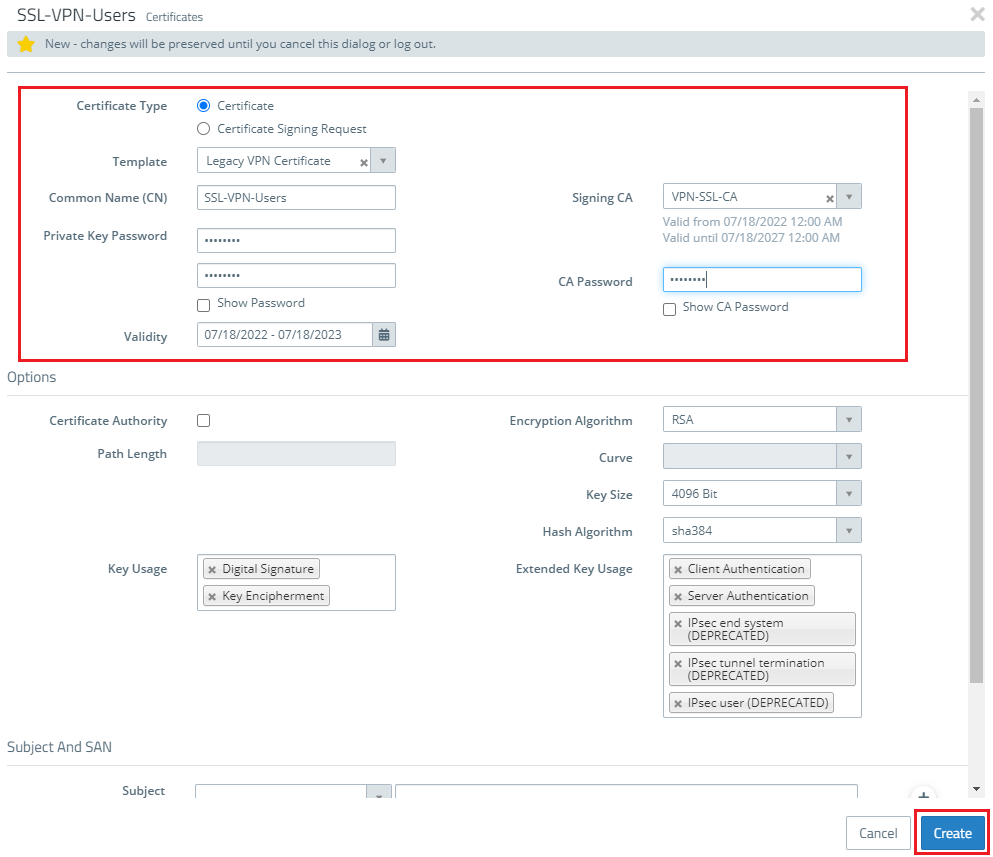
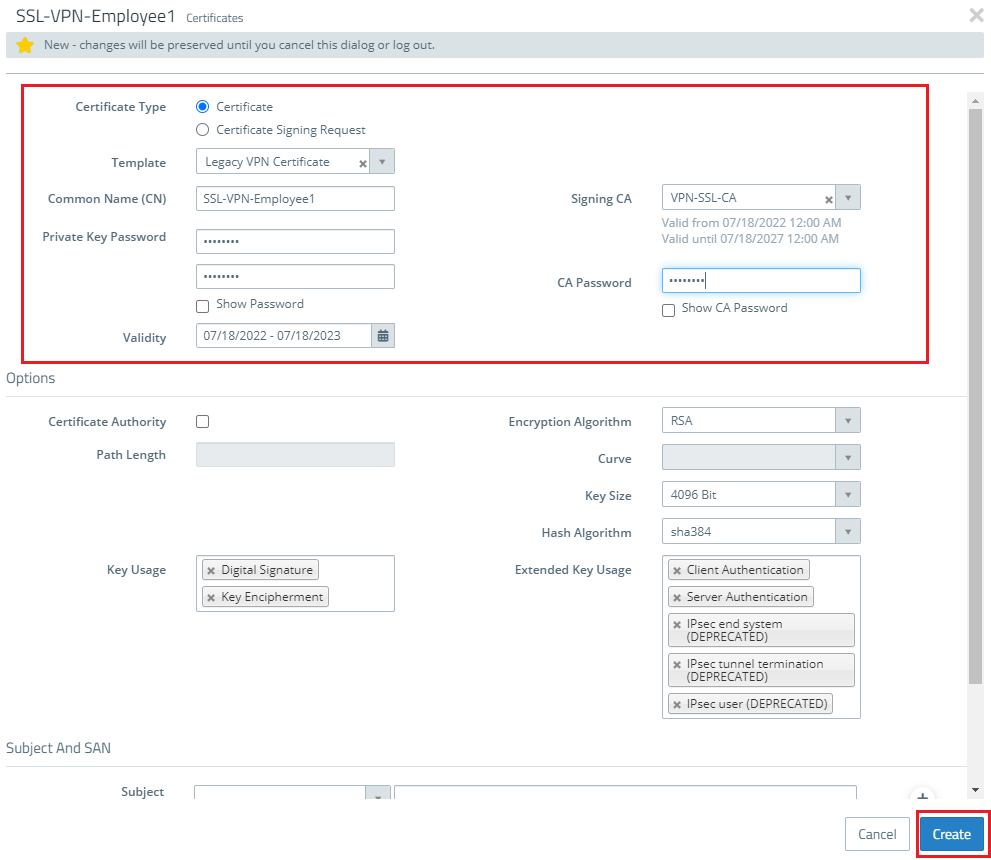
1.5) Create another certificate by clicking on the "+” icon.
1.6) Store the following parameters in order to create a VPN certificate, which is used to authenticate a particular employee or VPN client:
- Certificate type: Select Certificate.
- Template: Select the template Certificate Authority.
- Common Name (CN): Enter a descriptive common name.
- Private key password: Set a password. This is used to encrypt the private key.
- Validity: Specify how long the certificate should remain valid. For a CA, the period of validity is usually set to be very high.
- Signing CA: From the drop-down menu, select the CA created in step 1.2.
- CA password: Enter the private key password set in step 1.2.
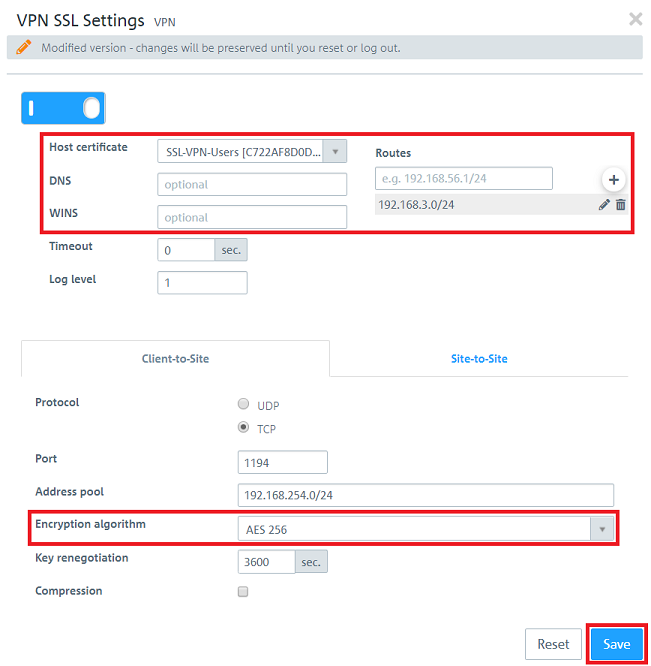
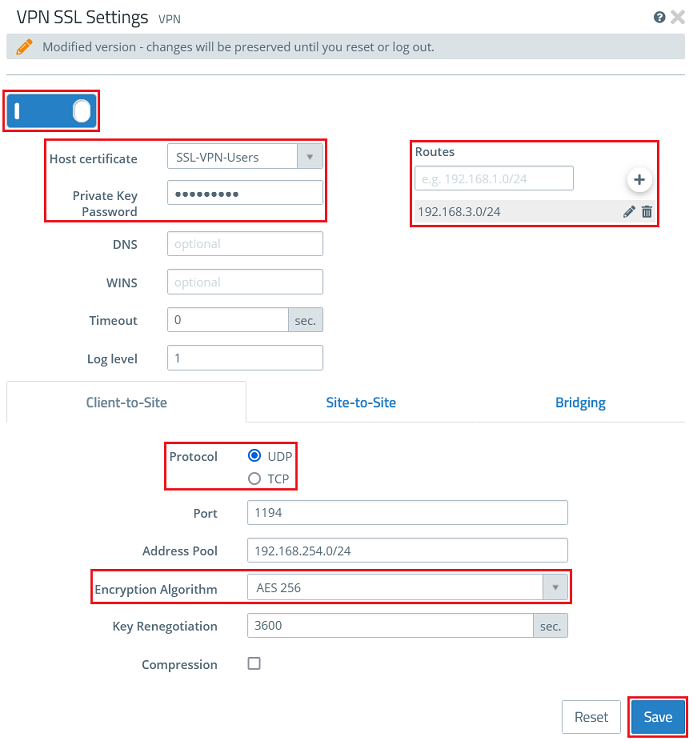
1.7) Switch to the menu VPN → VPN SSL → VPN SSL Settings
1.8) Enable the VPN SSL service and enter the following parameters:
- Host certificate: From the drop-down menu, select the VPN certificate created in step 1.4
...
- Private Key Password: Enter the private key password of the VPN certificate entered in step 1.4.
- Routes: The networks that the VPN client should communicate with should be entered in CIDR notation (Classless Inter-Domain Routing). These are shared with all of the VPN SSL clients.
- Protocol: Make sure, that the option UDP is selected. If TCP is used for the VPN SSL tunnel and data is transferred via TCP within the tunnel, this could lead to a "TCP meltdown".
- Encryption algorithm: From the drop-down menu, select AES256.
| Info |
|---|
Optionally you can enter a DNS and/or WINS server, which are assigned to all VPN SSL clients. If necessary, you can change the protocol and the portthe Port. The Address Pool is the range of IP addresses that are assigned to the dial-in VPN SSL clients. This address range must not already be in use as an internal network in the Unified Firewall. |
The address pool is the range of IP addresses that are assigned to the dial-in VPN SSL clients. This address range may not already be in use as an internal network in the Unified Firewall.
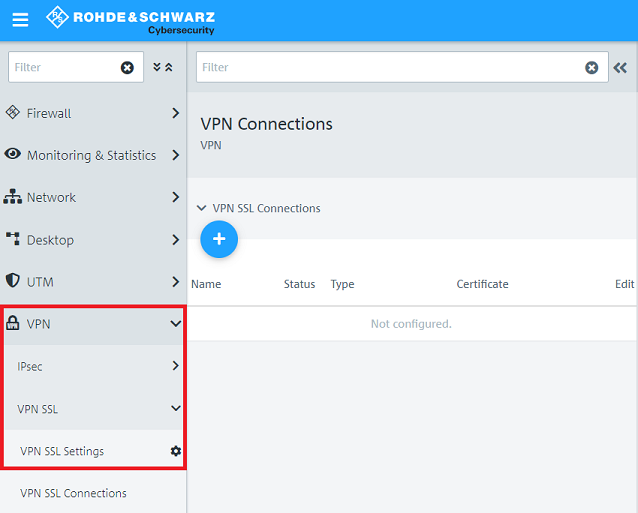
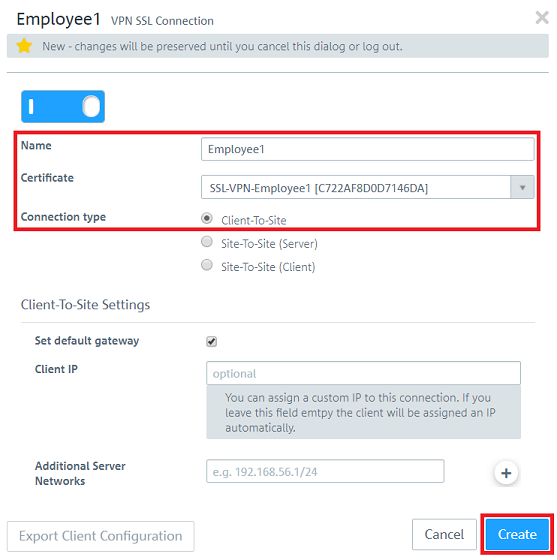
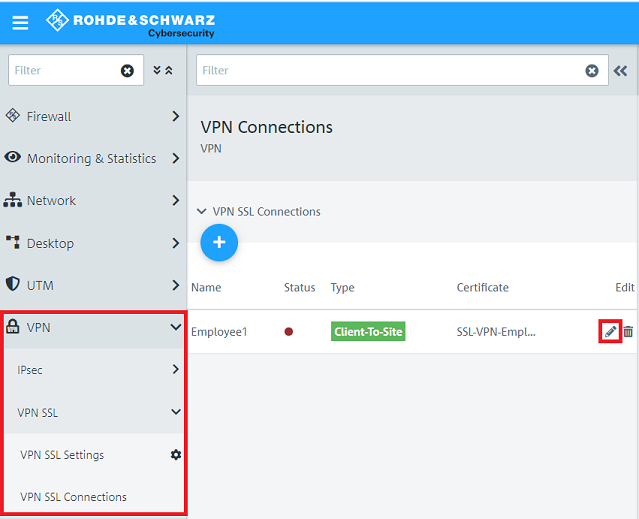
1.9) Change to the menu VPN → VPN SSL → VPN SSL Connections and click on the “+” icon to create a new VPN SSL connection.
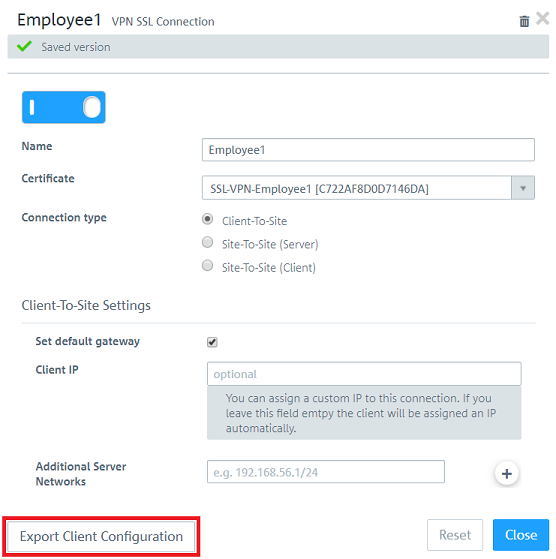
1.10) Enable the VPN connection and enter the following parameters:
- Name: Enter a descriptive name.
- Certificate: From the drop-down menu, select the VPN certificate for the employees created in step 1.6.
- Connection type: Choose Client-to-Site.
| Info |
|---|
With the function Set standard gateway activated, the VPN client can communicate with the Internet via the Internet connection of the Unified Firewall. The item Client IP allows a fixed IP address to be assigned to the VPN client. If this entry is left empty, the VPN client is given an IP address from the address pool (see step 1.8). Additional server networks optionally allows the VPN client to access other local networks. In this way, individual employees can be given access to different local networks. |
1.11) Edit the VPN SSL connection created in step 1.10 by clicking on the “pencil” icon.
1.12) Click Export client configuration to export the VPN profile together with the certificate.
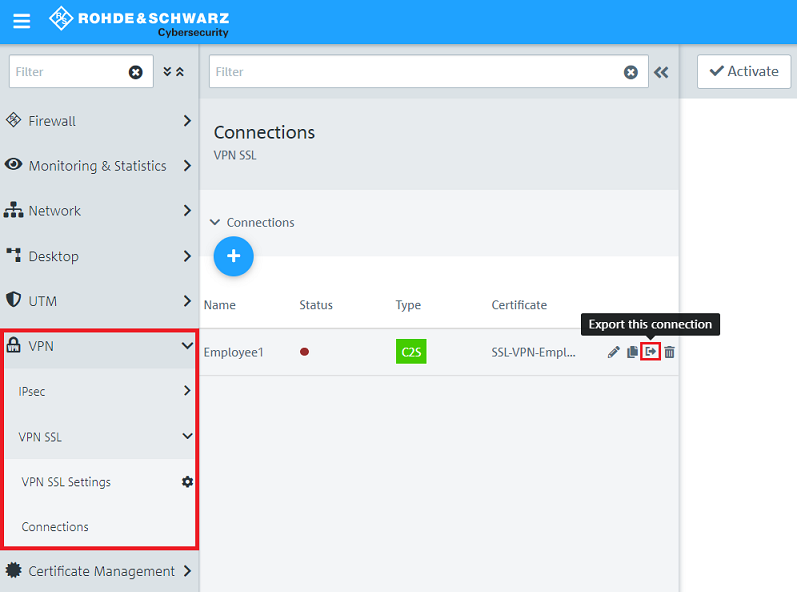
| Info |
|---|
As of LCOS FX 10.5 you can export the profile directly in the menu VPN → VPN SSL → Connections by clicking on the option Export this connection for a specific connection. It is possible that you have to click on the double arrow symbol first (right next to the field Filter) to expand the menu, so that the symbol for the profile export is visible. |
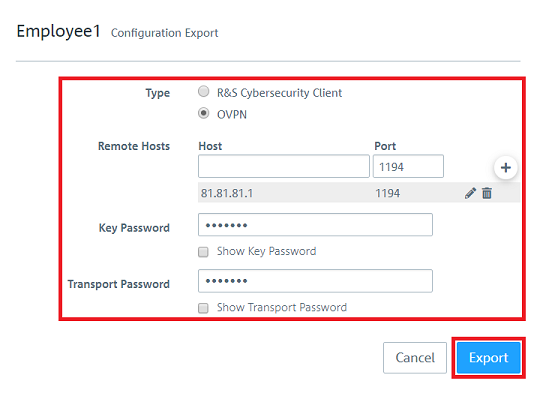
1.13) Enter the following parameters and then click on Export.
- Type: Select OVPN to generate a profile for the OpenVPN client.
- Remote Hosts: Enter the public IPv4 address or the DynDNS name of the Unified Firewall along with the VPN SSL port (see step 1.8).
- Key Password: Enter the private key password set in step 1.6.
- Transport Password: Set a password. This has to be entered when the user starts the VPN connection with the OpenVPN client.
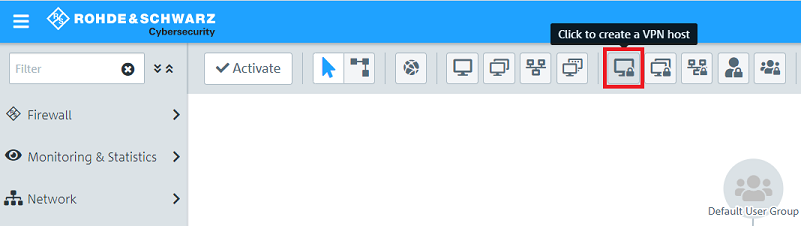
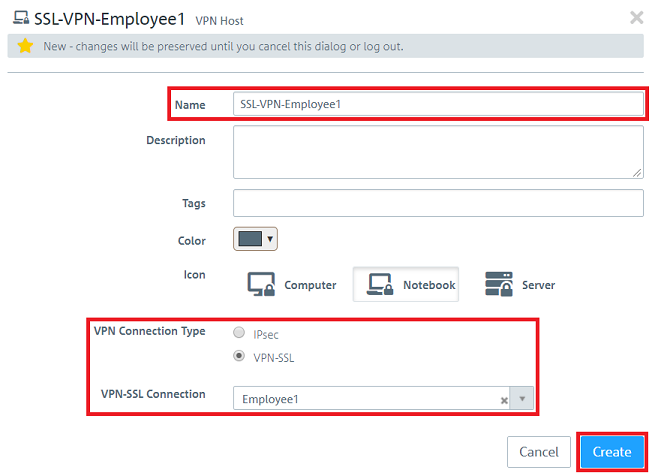
1.14) Click the button to create a new VPN host.
1.15) Save the following parameters:
- Name: Enter a descriptive name.
- VPN connection type: Select VPN-SSL.
- VPN SSL connection: From the drop-down menu, select the VPN SSL connection created in step 1.10
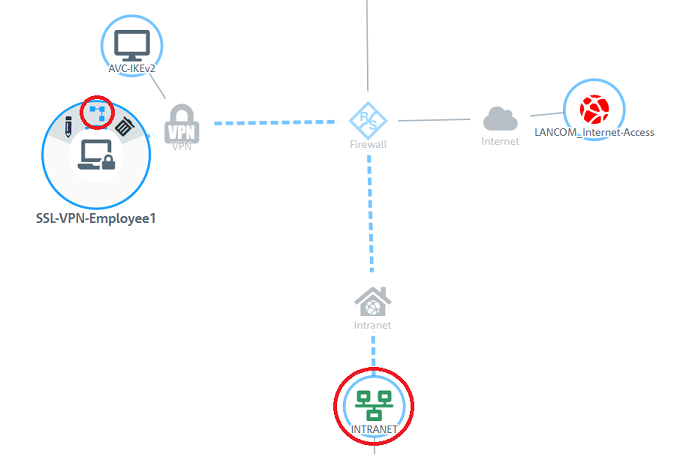
1.16) In the VPN host click on the "connection" icon and, to open the firewall objects, click on the network object that the OpenVPN client should access.
Repeat this step for every network that the OpenVPN client should be able to access.
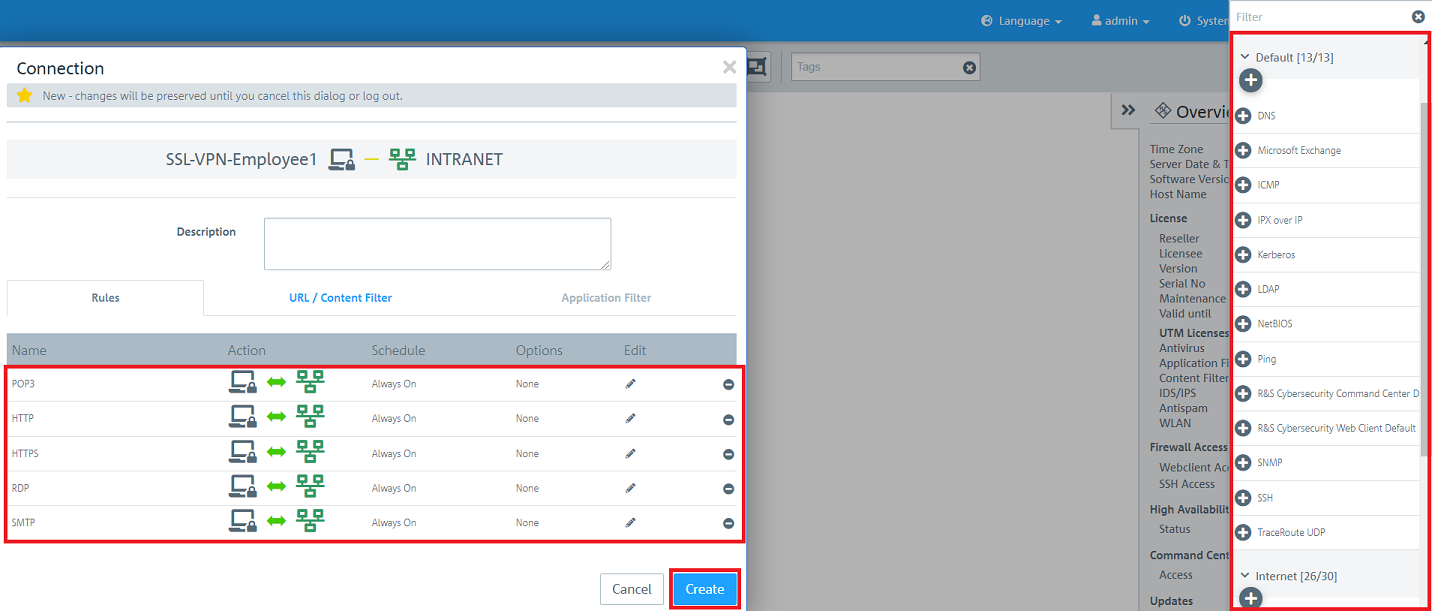
1.17) Use the “+” sign to assign the required protocols to the VPN host.
| Info |
|---|
| A Unified Firewall uses a deny-all strategy. You therefore have to explicitly allow communication. |
| Info |
|---|
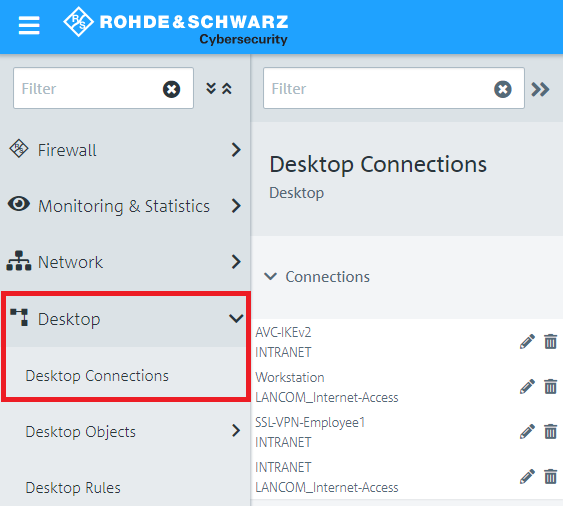
| Firewall objects can also be accessed via Desktop→ Desktop connections and clicking on the “pencil” icon for editing. |
1.19) This concludes the configuration steps on the Unified Firewall.
2) Configuration steps in the OpenVPN client under iOS:
2.1) Open the OpenVPN app and select the option Import profile.
2.2) Choose one of the types of profile import available in the app and import the client configuration exported in step 1.12.
2.3) After a successful import the profile is shown in the profile list and can be connected by using the adjacent switch.
2.4) This concludes the configuration steps in the OpenVPN client.
3) Setting up port and protocol forwarding on a LANCOM router (scenario 2 only):
IPSec requires the use of the UDP ports 500 and 4500 as well as the protocol ESP. TheseVPN SSL uses the UDP port 1194 by default. It must be forwarded to the Unified Firewall
.Forwarding the UDP ports 500 and 4500 automatically causes the ESP protocol to be forwarded.
| Info |
|---|
| If you are using a router from another manufacturer, ask them about appropriate procedure. |
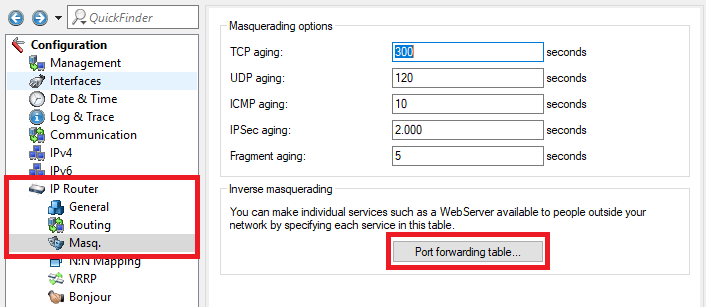
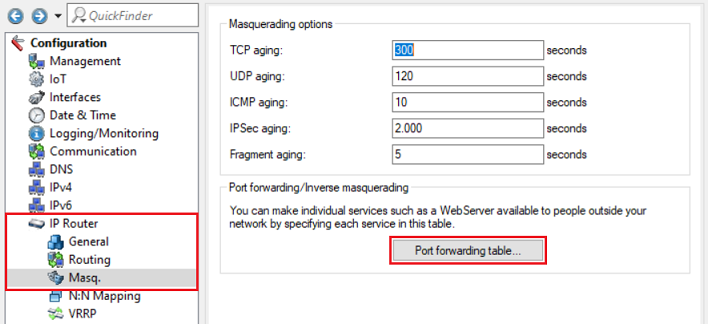
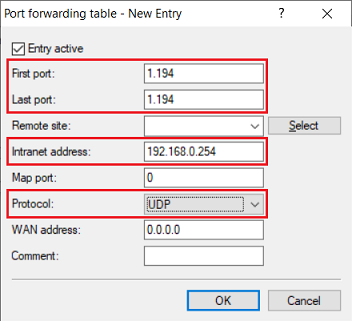
3.1) Open the configuration for the router in LANconfig and switch to the menu item IP-Router -> → Masq. -> → Port forwarding table.
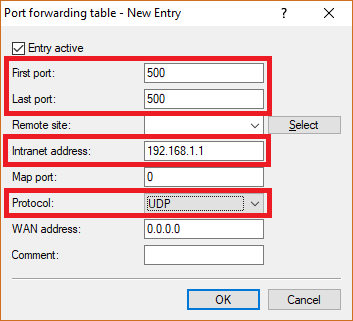
3.2) Save the following parameters:
- First port: Specify the Port 5001194.
- Last port: Specify the Port 5001194.
- Intranet address: Specify the IP address of the Unified Firewall in the transfer network between the Unified Firewall and the LANCOM router.
- Protocol: From the drop-down menu, select UDP.
3.3) Create a further entry and specify the UDP port 4500.
3.4) Write the configuration back to the router.