Description:
This document describes how to set up an IKEv2 connection between the LANCOM Advanced VPN Client and a LANCOM R&S®Unified Firewall (referred to here as the United Firewall).
Requirements:
- LANCOM R&S® Unified Firewall with LCOS FX as of version 10.7
- LANCOM Advanced VPN Client as of version 4.1
- A configured and functional Internet connection on the Unified Firewall
- Web browser for configuring the Unified Firewall.
The following browsers are supported:- Google Chrome
- Chromium
- Mozilla Firefox
Scenario :
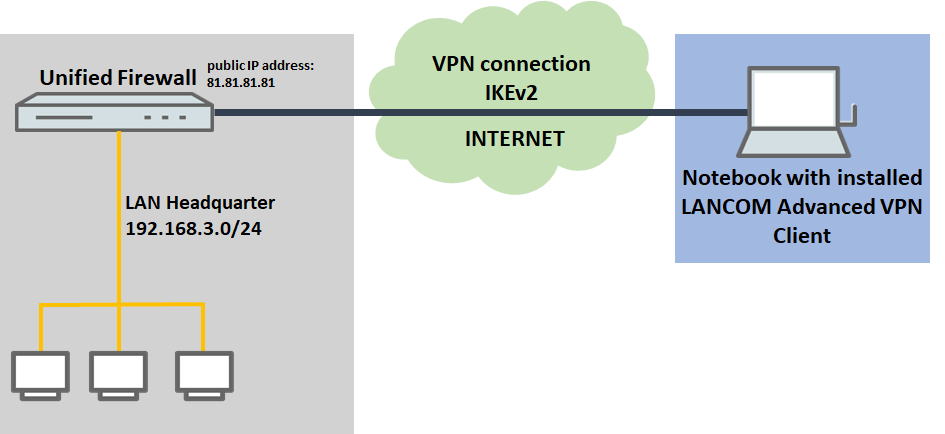
1) The Unified Firewall is connected directly to the Internet and has a public IPv4 address:
- A company wants its sales representatives to have access to the corporate network via an IKEv2 client-to-site connection.
- The notebooks used by the sales representatives have the LANCOM Advanced VPN Client installed on them.
- The company headquarters has a Unified Firewall as a gateway with an Internet connection with the fixed public IP address 81.81.81.81.
- The local network at the headquarters has the IP address range 192.168.3.0/24.
- The VPN connection should be authenticated using certificates. The CA of the Unified Firewall is used.
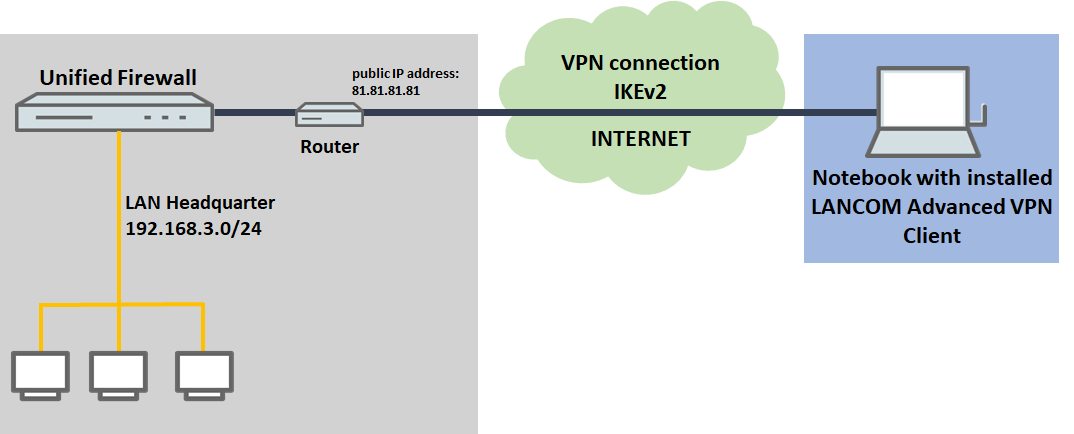
2) The Unified Firewall is connected to the Internet via an upstream router:
- A company wants its sales representatives to have access to the corporate network via an IKEv2 client-to-site connection.
- The notebooks used by the sales representatives have the LANCOM Advanced VPN Client installed on them.
- The company headquarters has a Unified Firewall as the gateway and an upstream router for the Internet connection. The router has the fixed public IP address 81.81.81.81.
- The local network at the headquarters has the IP address range 192.168.3.0/24.
- The VPN connection should be authenticated using certificates. The CA of the Unified Firewall is used.
Procedure:
The setup for scenarios 1 and 2 are basically the same. Scenario 2 additionally requires port and protocol forwarding to be set up on the upstream router (see section 6).
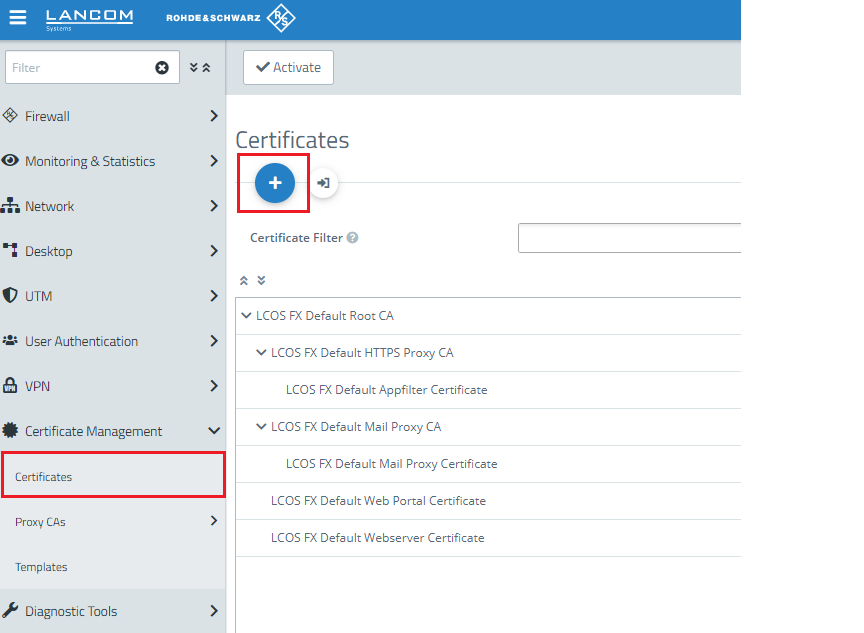
1) Creating the CA and VPN certificates on the Unified Firewall:
1.1) Click on the "+" icon to create a new routing entry.
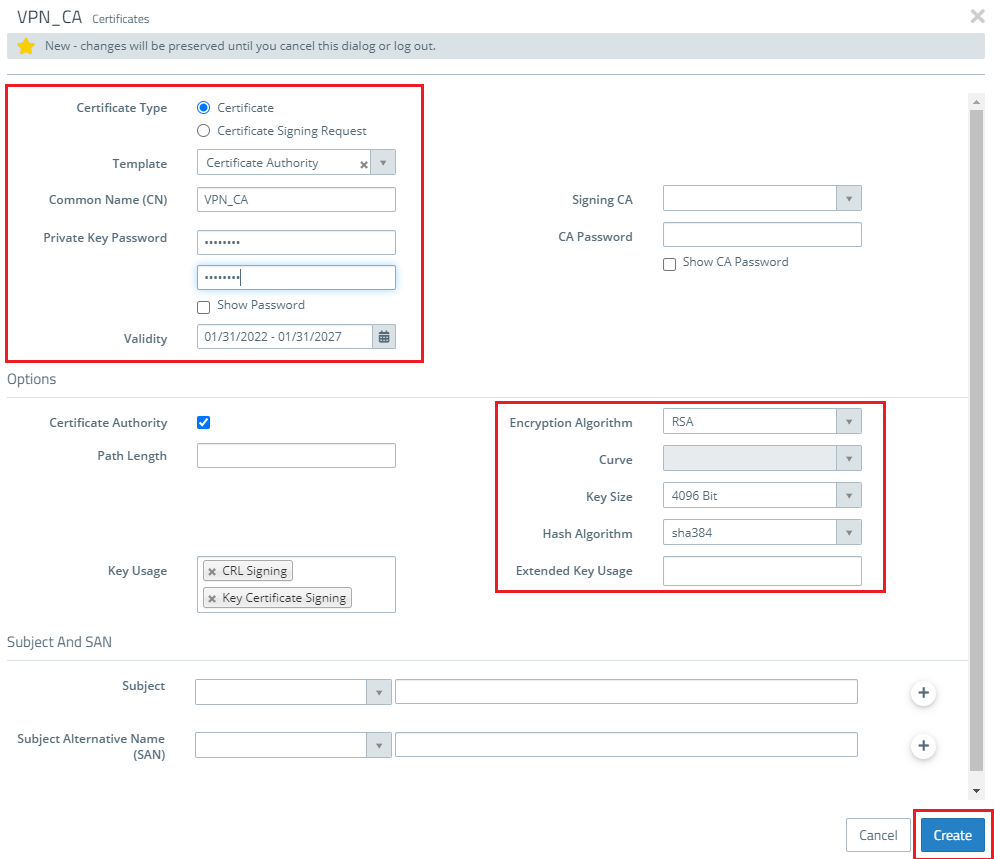
1.2) The first step is to create a Certification Authority (CA) for VPN connections.
- For the Certificate type, select Certificate.
- Certificate Authority must be selected as the template.
- Enter any Common Name.
- Assign any private key password.
- Set a validity period.
- You can leave the settings Encryption Algorithm, Key Size and Hash Algorithm in the default.
1.3) Then click the Create button.
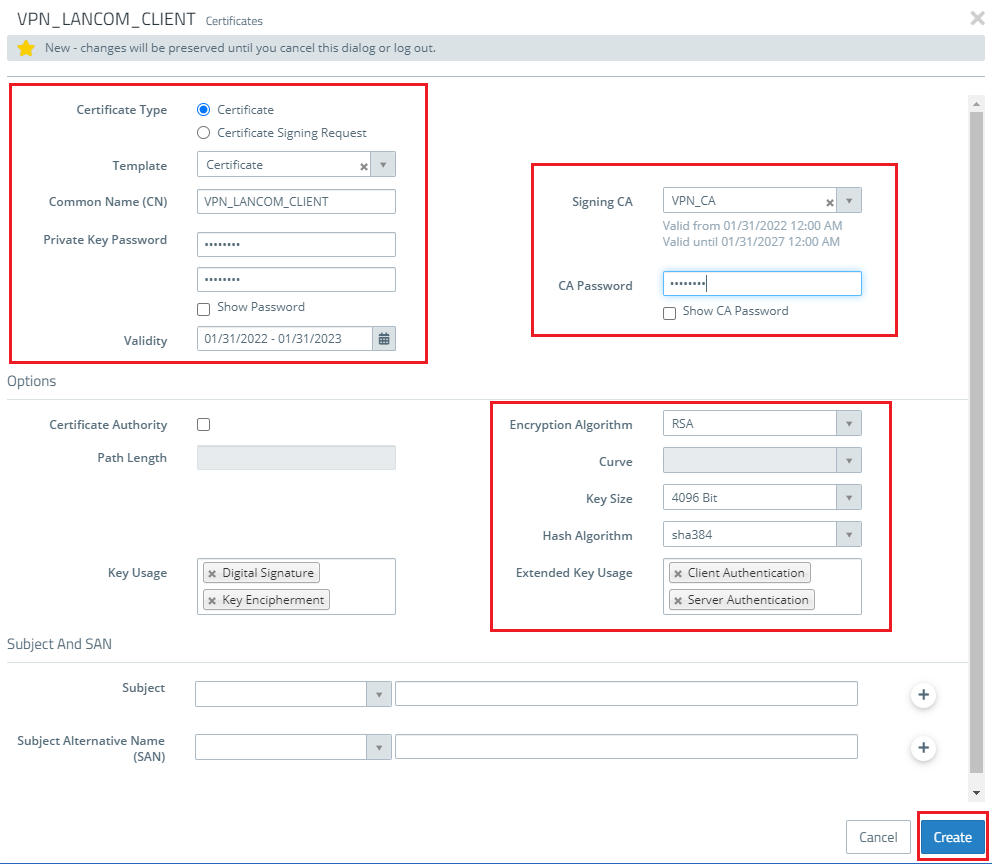
1.4) Click on the "+" icon to create a VPN certificate for the LANCOM Advanced VPN Client:
- For the Certificate type, select Certificate.
- Certificate must be selected as the template.
- Assign any private key password.
- Set a validity period.
- Select the VPN CA from step 1.2 as the "Signing CA".
- In the CA password field, enter the password that you assigned in step 1.2.
- You can leave the settings Encryption Algorithm, Key Size and Hash Algorithm in the default.
1.5) Then click the Create button.
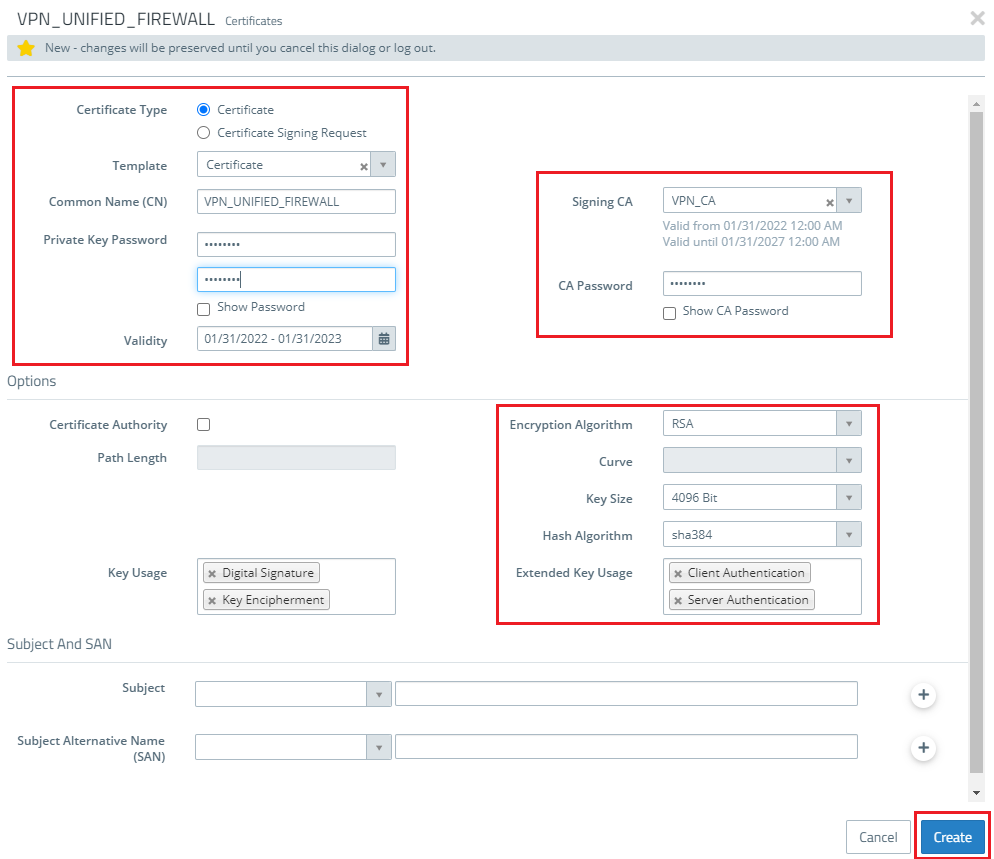
1.6) Click on the "+" icon to create a certificate for the Unified Firewall:
- For the Certificate type, select Certificate.
- Certificate must be selected as the template.
- Assign any private key password.
- Set a validity period.
- Select the VPN CA from step 1.2 as the "Signing CA".
- In the CA password field, enter the password that you assigned in step 1.2.
- You can leave the settings Encryption Algorithm, Key Size and Hash Algorithm in the default.
- CA Password and Private Key Password, enter the password set in step 1.2.
1.7) Then click the Create button.
2) Creating the VPN connection on the Unified Firewall:
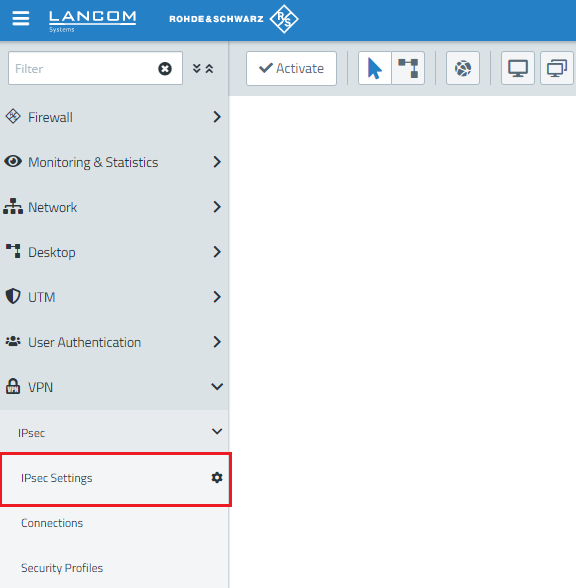
2.1) Connect to the configuration interface of the Unified Firewall and navigate to VPN → IPsec settings.
2.2) Activate IPsec.
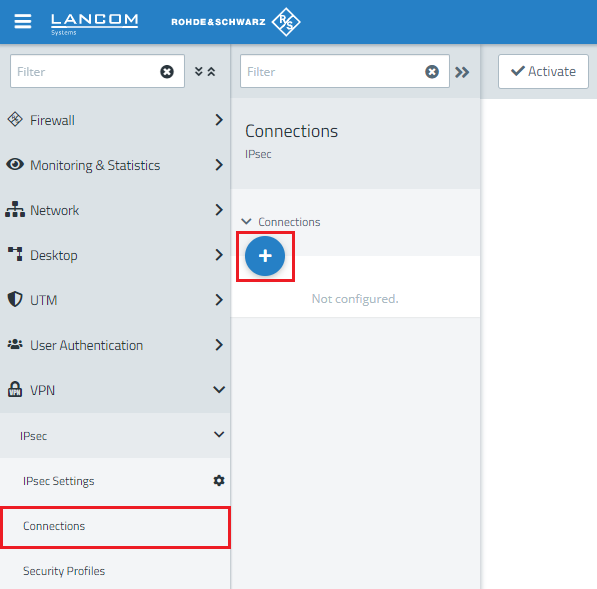
2.3) Switch to VPN → IPsec Connections and click on the "+" icon to create a new IPsec connection.
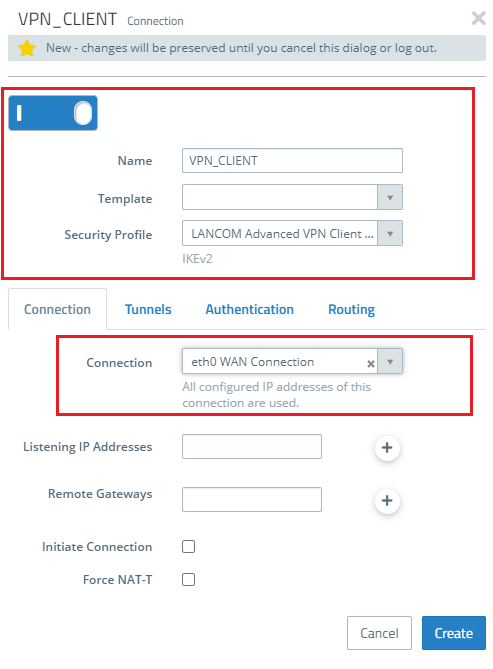
2.4) Save the following parameters:
- Name: Enter a descriptive name.
- Security profile: Here you select the ready-made profile LANCOM Advanced VPN Client IKEv2 X.509.
- Connection: Select your configured Internet connection.
If you have created your own template or security profile , you can use these here.
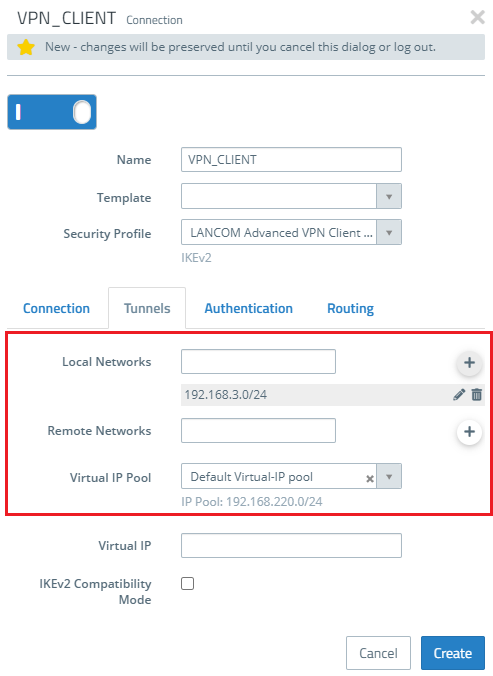
2.5) Open the Tunnels tab.
- Local networks: Here you enter the local networks (in CIDR notation) that the VPN client should reach. In this example, the local network at the headquarters has the IP address range 192.168.3.0/24.
- Virtual IP pool: Select the option Default virtual IP pool. Virtual IP pools can be used to send IP address configurations to connected VPN clients.
If an IP address from a local network should be assigned to the VPN client instead of an address from the Virtual IP Pool (via the field Virtual IP), Route-based IPSec has to be activated and a routing entry for the VPN interface has to be created in the Routing Table 254 which refers to the virtual IP address in the local network.
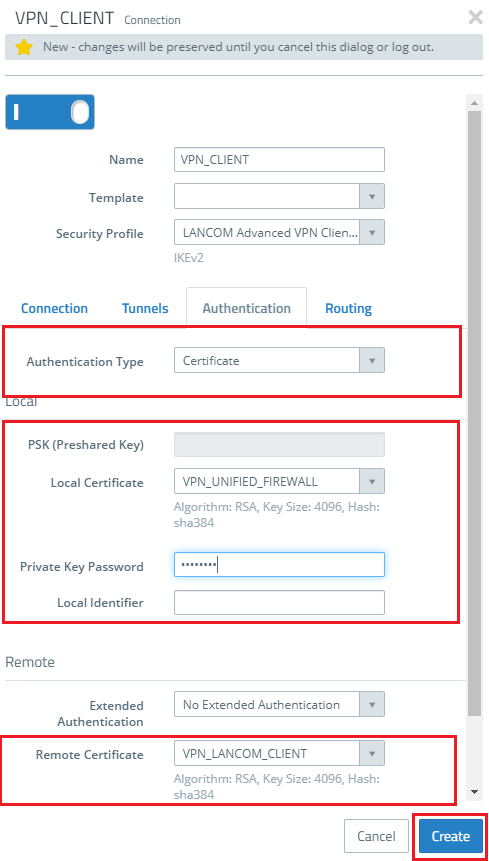
2.6) Change to the Authentication tab and enter the following parameters:
- Authentication type: Select the option Certificate here.
- Local certificate: Here you select the VPN certificate created for the Unified Firewall in step 1.6.
- Private Key Password: Enter the password assigned in step 1.6.
- Remote certificate: Here you select the VPN certificate here created for the LANCOM Advanced VPN Client in step 1.4.
2.7) Click on Create to save the configuration.
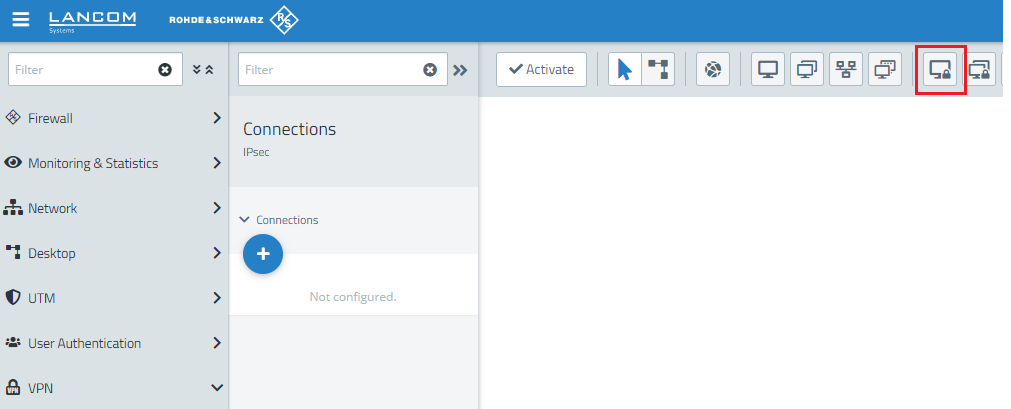
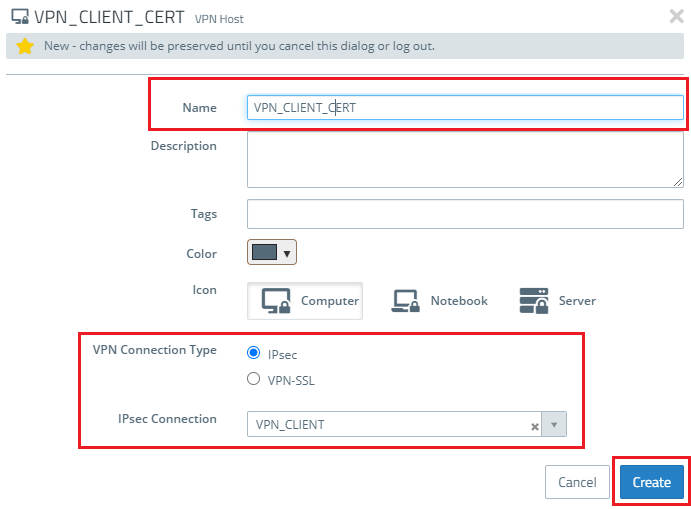
2.8) Click the icon to create a new VPN host.
2.9) Save the following parameters:
- Name: Enter a descriptive name.
- VPN connection type: Select the type IPsec.
- IPsec connection: From the drop-down menu under IPsec, select the VPN connection created in steps 2.4 - 2.7.
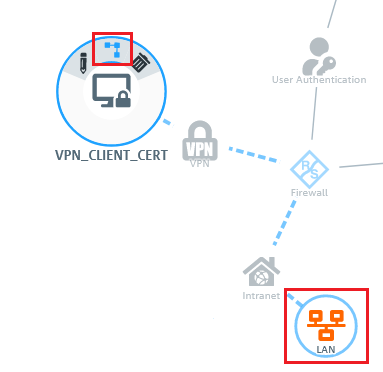
2.10) In the VPN host click on the "connection" icon and, to open the firewall objects, click on the network object that the object (the site-to-site connection) should access.
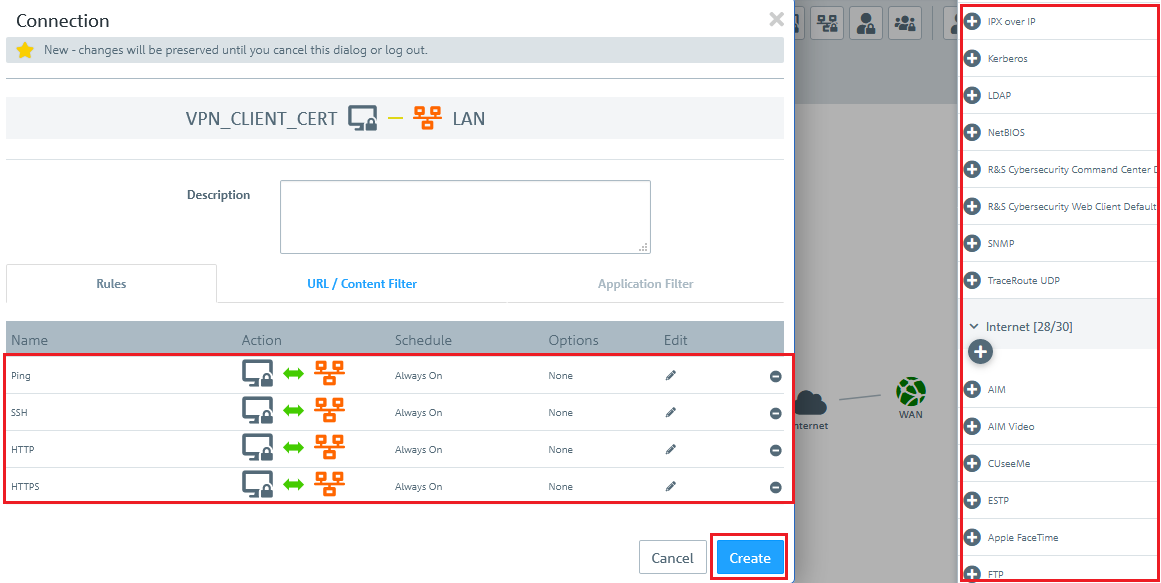
2.11) Use the "+" sign to assign the required protocols to the VPN host.
A Unified Firewall uses a deny-all strategy. You therefore have to explicitly allow communication.
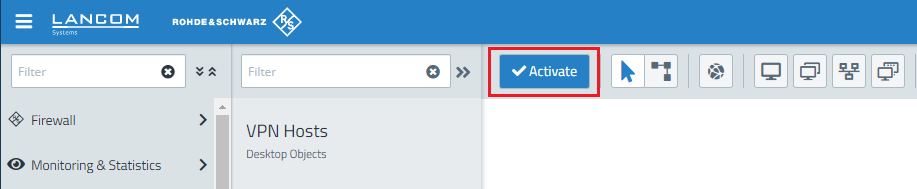
2.12) Finally, implement the configuration changes by clicking Activate in the firewall.
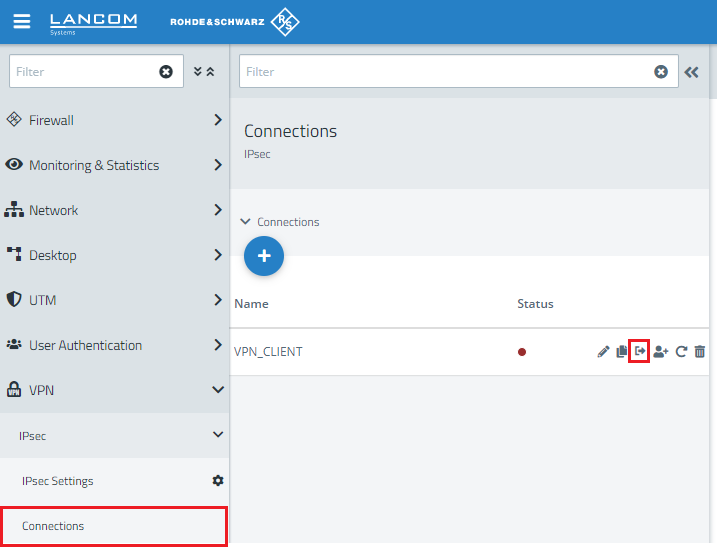
2.13) Change to the menu VPN → IPsec → Connections and, on the newly created Advanced VPN Client connection, click on the Export connection button.
2.14) Enter a password to be used to encrypt the exported ZIP archive.
2.15) In the Gateway field, enter the public IP or DNS address of the Unified Firewall (in this case 81.81.81.81).
2.16) As Key password you enter the one entered in step 1.4 as the Private Key Password for the VPN certificate for the LANCOM Advanced VPN Client.
2.17) Set any transport password.
2.18) Click Export and save the ZIP file on your computer.
3) Export the VPN certificate for the LANCOM Advanced VPN Client:
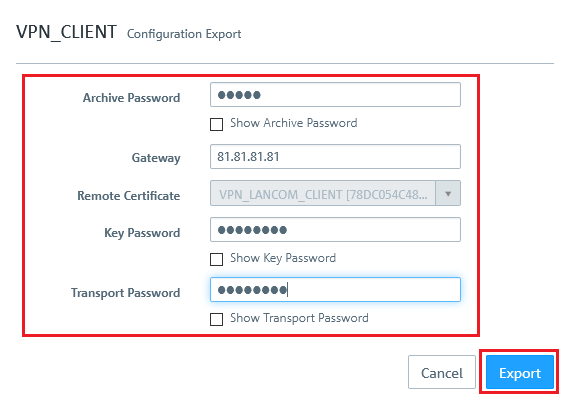
3.1) Change to the menu Certificate Management → Certificates and, for the VPN certificate for the LANCOM Advanced VPN Client, click the Export button.
3.2) Set that PKCS 12 format.
3.3) Enter the password for the Private Key Password entered in step 1.4.
3.4) Set any transport password. You will need this in step 4.1 to unzip the ZIP file.
3.5) Click Export and save the certificate file on your PC.
3.6) This concludes the configuration steps on the Unified Firewall.
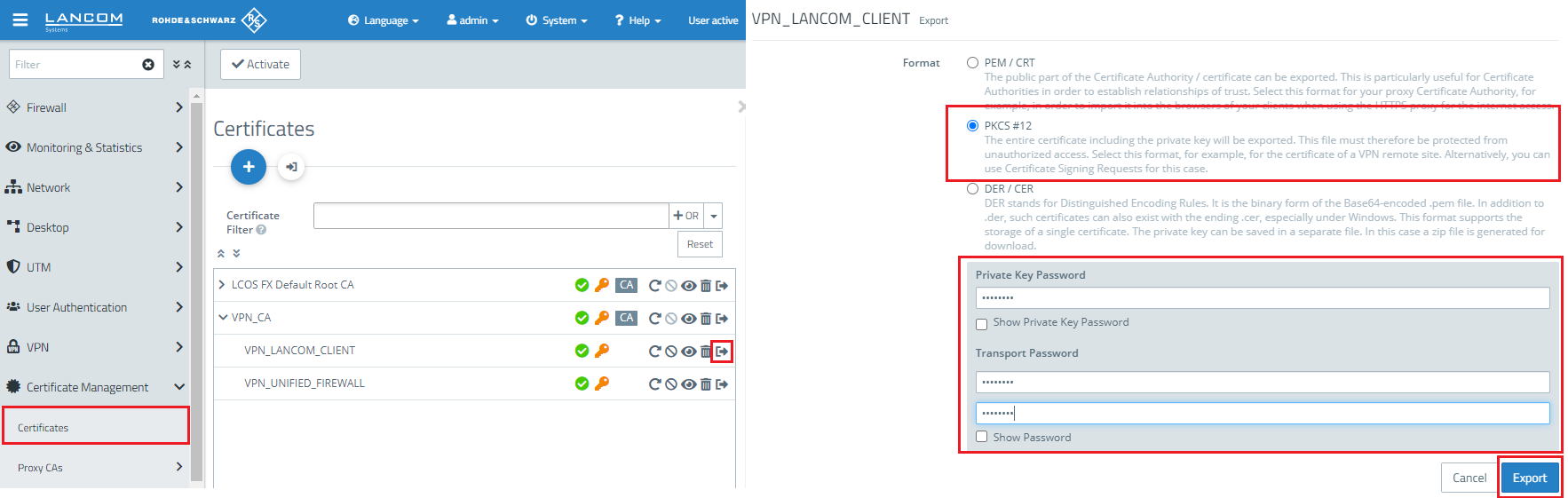
4) Import the VPN client certificate into the LANCOM Advanced VPN Client:
4.1) Unzip the ZIP file on your PC and copy the *.p12 file to a directory of your choice.
4.2) In the LANCOM Advanced VPN Client, open the option Configuration → Certificates.
4.3) Create a new certificate configuration using the Add button.
4.4) Enter a name for the new certificate configuration.
- In the Certificate field, select the option from PKCS#12 file
- In the PKCS#12 file name field, set the path to the certificate file for the VPN client.
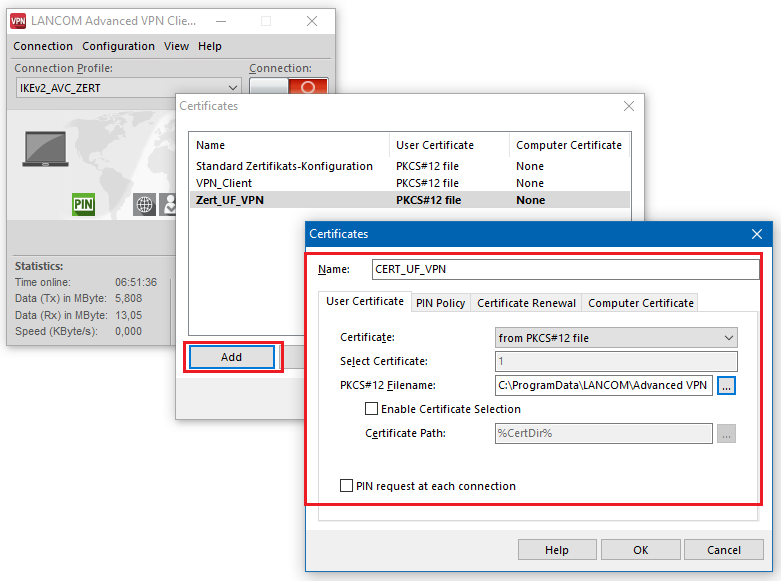
5) Import the *.ini file and the configuration of the VPN connection into the LANCOM Advanced VPN Client:
5.1) Unzip the ZIP file exported in step 2.13.
5.2) In the LANCOM Advanced VPN Client open the option Configuration → Profiles and click Add/import.
5.3) Select the option Profile import.
5.4) Set the PATH to the VPN profile file.
5.5) Click on Finish to conclude the import.
5.6) Select the imported profile and then click Next.
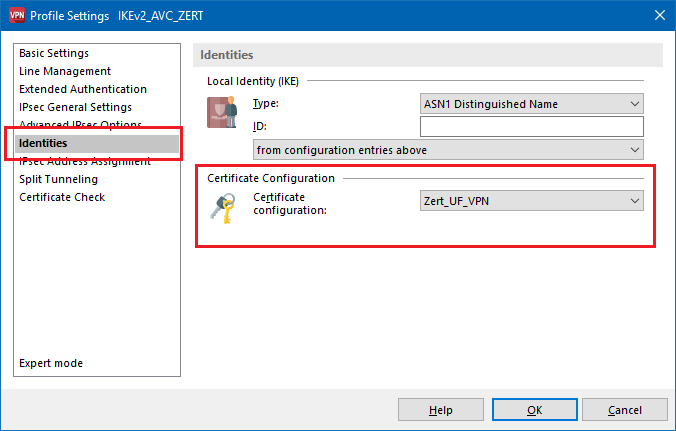
5.7) Switch to the menu IPsec general settings and set IKEv2 authentication to the value Certificate.
5.8) You need to set the Certificate configuration to the certificate configuration created in step 4.3.
5.9) This concludes the configuration. Close the dialogs of the LANCOM Advanced VPN Client with OK.
5.10) When establishing the connection, the PIN to enter is the Transport Password of the Client certificate (see step 3.4).
6) Setting up port and protocol forwarding on a LANCOM router (scenario 2 only):
IPSec requires the use of the UDP ports 500 and 4500 as well as the protocol ESP. These must be forwarded to the Unified Firewall.
Forwarding the UDP ports 500 and 4500 automatically causes the ESP protocol to be forwarded.
If you are using a router from another manufacturer, ask them about appropriate procedure.
If the UDP ports 500 and 4500 and the ESP protocol are forwarded to the Unified Firewall, an IPSec connection to the LANCOM router can only be used if it is encapsulated in HTTPS (IPSec-over-HTTPS). Otherwise, no IPSec connection will be established.
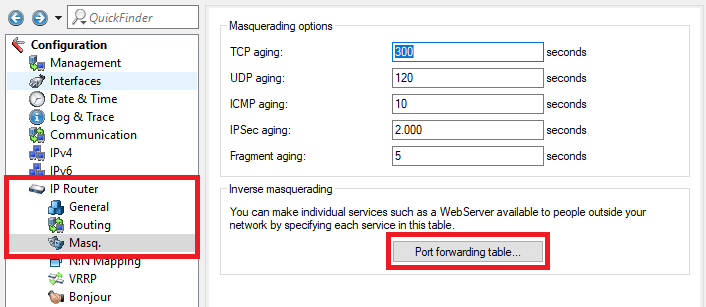
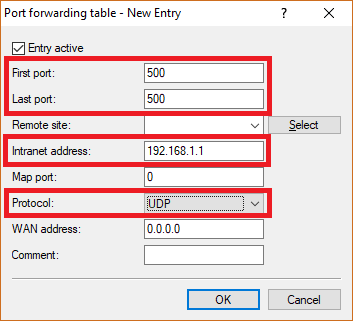
6.1) Open the configuration for the router in LANconfig and switch to the menu item IP-Router → Masq . → Port forwarding table .
6.2) Save the following parameters:
- First port : Specify the Port 500.
- Last port : Specify the Port 500.
- Intranet address : Specify the IP address of the Unified Firewall in the transfer network between the Unified Firewall and the LANCOM router.
- Protocol: From the drop-down menu, select UDP.
6.3) Create a further entry and specify the UDP port 4500.
6.4) Write the configuration back to the router.